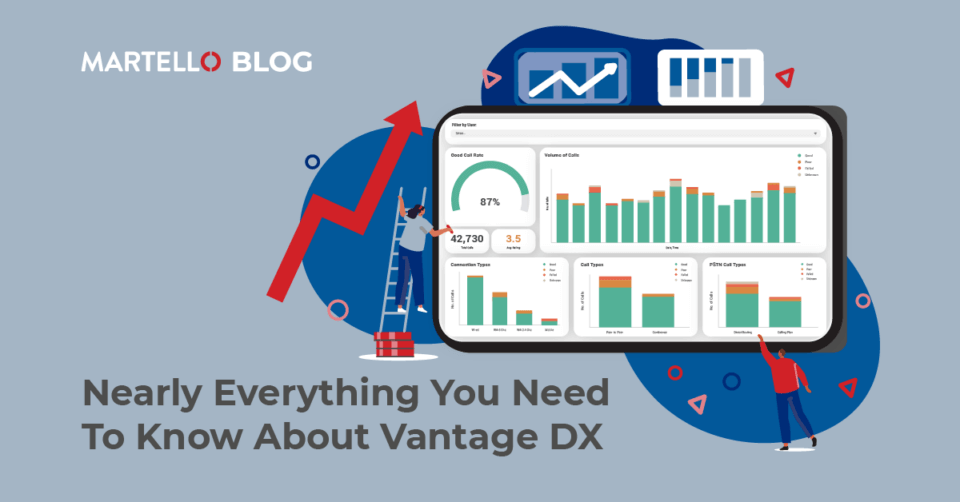
Nearly Everything You Need To Know About Vantage DX
Microsoft Teams MonitoringVantage DX, the only Experience Management Solution purpose-built for Microsoft Teams. This might well be your first-time hearing about Vantage DX. If it is…welcome! We’re here to help enterprises improve their communication and collaboration by giving them the tools they need to understand what is and isn’t working with their Microsoft Teams setup. Here’s just …